Microsoft released an emergency security update on Tuesday for its ASP.NET Core framework, addressing a high-severity vulnerability that could allow unauthenticated attackers to seize full system-level control of Linux and macOS machines running affected web applications.
Microsoft has issued an out-of-cycle security patch for ASP.NET Core after researchers identified a critical flaw that exposes servers running Linux and macOS to complete compromise by unauthenticated attackers.
The vulnerability, tracked as CVE-2026-40372, affects versions 10.0.0 through 10.0.6 of the Microsoft.AspNetCore.DataProtection NuGet package — a core component of the ASP.NET framework widely used to build and host web applications. Microsoft disclosed the issue via GitHub on Tuesday evening.
How the Attack Works
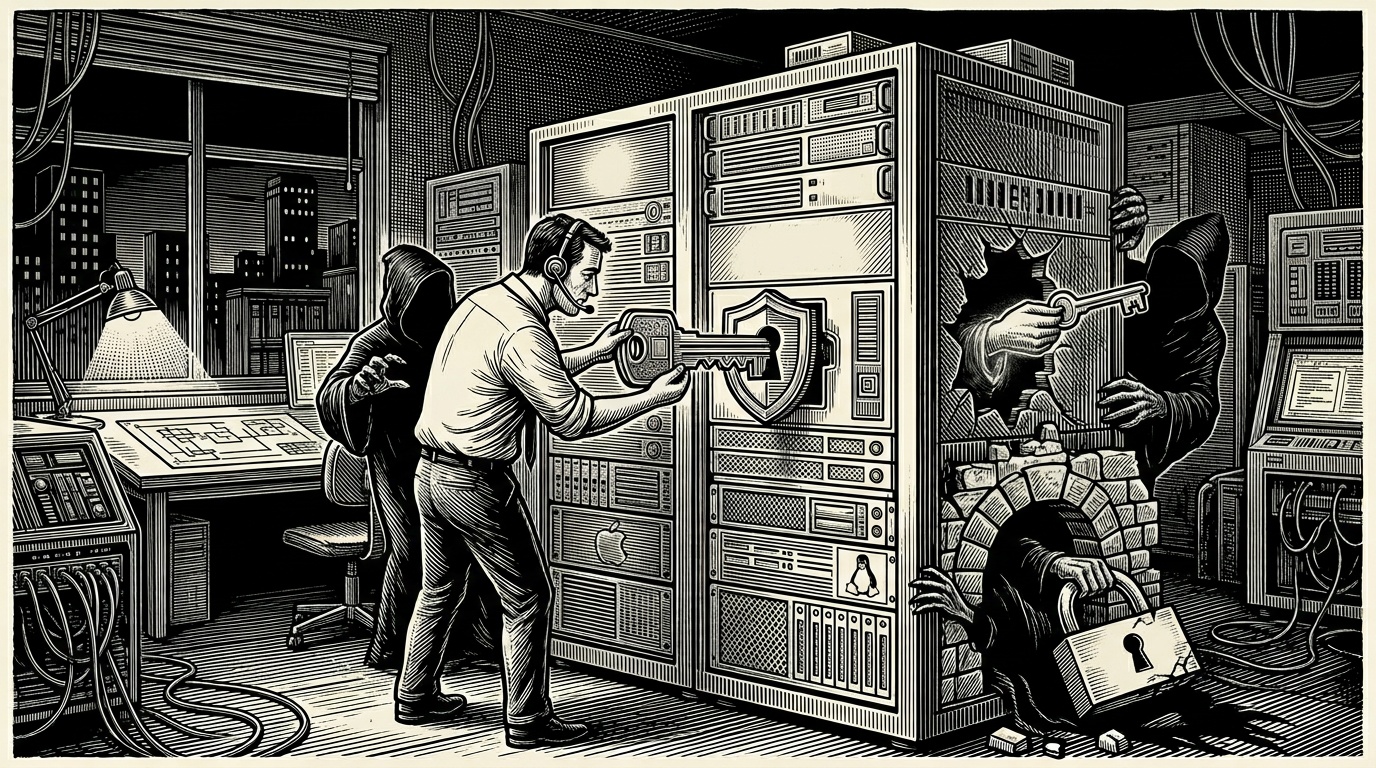
At the heart of the vulnerability is a flaw in how the package verifies cryptographic signatures. Specifically, the bug undermines the HMAC (Hash-based Message Authentication Code) validation process, which is the mechanism responsible for confirming the integrity and authenticity of data exchanged between a client and server.
By exploiting this weakness, an attacker with no prior authentication can forge authentication payloads and trick the server into granting them SYSTEM-level privileges — the highest level of access on the underlying machine. This would give an attacker the ability to read or modify any file, install malware, create backdoor accounts, or otherwise fully compromise the affected system.
Notably, the vulnerability only affects Linux and macOS deployments of the framework. Windows environments running ASP.NET Core are not impacted by this particular flaw.
Patching Is Necessary but Not Sufficient
Microsoft has warned administrators of a particularly concerning complication: installing the patch alone may not fully remediate a system that has already been targeted. If an attacker exploited the vulnerability before the patch was applied and created forged authentication credentials, those credentials remain valid even after the update is installed.
This means that organisations running affected versions must not only apply the emergency update but also audit their systems for signs of intrusion and actively purge any authentication tokens or credentials that may have been generated during the vulnerable window.
Microsoft has not publicly confirmed whether the vulnerability has been actively exploited in the wild, but the decision to issue an emergency — rather than scheduled — patch suggests the company assessed the risk as urgent.
Who Is Affected
Any developer or organisation using versions 10.0.0 to 10.0.6 of the Microsoft.AspNetCore.DataProtection package on a Linux or macOS host should treat this as a priority update. ASP.NET Core is broadly used across enterprise web development, meaning the potential attack surface is substantial.
Administrators are advised to update to the patched version of the NuGet package immediately, review server logs for anomalous authentication activity, and rotate or invalidate any authentication tokens generated during the period when vulnerable versions were in use.
Analysis
Why This Matters
- Unauthenticated remote exploitation for full system access represents one of the most severe classes of vulnerability possible — any internet-facing ASP.NET Core application on Linux or macOS could have been a target.
- The persistence of forged credentials after patching raises the stakes significantly: organisations must treat this as a potential incident response situation, not just a routine update.
- ASP.NET Core's widespread enterprise adoption means the affected surface spans thousands of production systems globally.
Background
ASP.NET Core is Microsoft's open-source, cross-platform web development framework, first introduced in 2016 as a modernised successor to the Windows-only ASP.NET. Its expansion to Linux and macOS made it attractive to a new generation of cloud-native and DevOps-oriented teams, dramatically widening its deployment footprint beyond traditional Windows server environments.
Data protection and cryptographic integrity are foundational to web security. HMAC validation, the mechanism undermined by this flaw, is a well-established standard used to ensure that data — including authentication tokens and session cookies — has not been tampered with. A failure in this layer effectively voids the trust model of any application relying on it.
Microsoft regularly patches .NET and ASP.NET as part of its monthly Patch Tuesday cycle. Out-of-band emergency patches of this kind are reserved for vulnerabilities deemed too severe or time-sensitive to wait for the next scheduled release, signalling elevated concern within the company's security teams.
Key Perspectives
Microsoft: The company acknowledged the vulnerability and moved quickly with an emergency release, providing technical detail via GitHub. However, it has not publicly confirmed whether active exploitation has been observed, leaving administrators to gauge urgency without full threat intelligence.
Enterprise IT and DevOps Teams: For organisations running ASP.NET Core in Linux-based cloud or containerised environments, this flaw requires immediate action. The added burden of post-patch credential auditing means the remediation effort extends well beyond a simple package update.
Security Researchers: The nature of the flaw — a cryptographic verification bypass enabling privilege escalation without authentication — represents a serious design-level failure. Security professionals will likely scrutinise the broader DataProtection library for related weaknesses in the coming weeks.
What to Watch
- Whether Microsoft or independent security firms confirm active in-the-wild exploitation of CVE-2026-40372 in the days following disclosure.
- How quickly NuGet package managers and automated dependency tools propagate the patched version across affected codebases.
- Any follow-on advisories indicating related vulnerabilities in adjacent ASP.NET Core components, as cryptographic implementation flaws often cluster.